Products
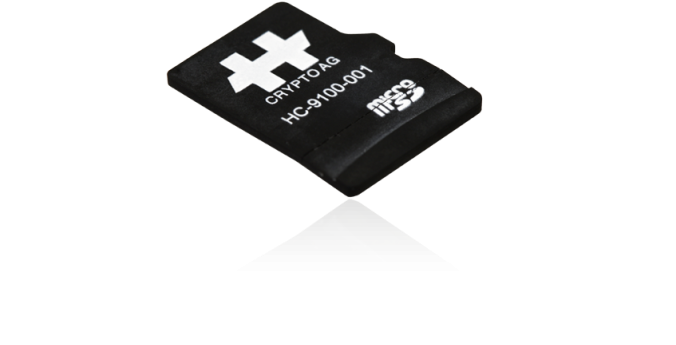
Crypto Mobile HC-9100
Crypto Mobile HC-9100 from Crypto International AG is a complete universal encryption platform in the format of a microSD card with impressive performance capabilities. As part of the unique Crypto security architecture, encryption is performed in a hardware processor integrated in the microSD card. The integrated Flash memory is also controlled and protected by this processor.
The Crypto Mobile HC-9100 is compatible with the high-performance smartphones Samsung Galaxy S4 Mini and Samsung GALAXY A3 as well as a number of phones from Nokia. You simply insert the card into the existing memory card slot – it will remain invisible to others. The Voice Encryption Mobile HA-2410 for Samsung and the Voice Encryption Mobile HA-2400 for Nokia models is a security application specially developed to allow the use of the sophisticated security functions in the HC-9100 with mobile phones. The interplay of the two products protects your voice communication reliably and to the maximum extent. If your mobile phone should fall into the wrong hands or be stolen, no one can access the data stored on the card. With the Crypto Mobile HC-9100, you own the smallest high-security encryption platform in the world.
Features
- High-security, hardware-based encryption.
- Small, high-performance micro-SD card with a processor developed by Crypto International AG.
- Crypto security architecture with tamper-proof design.
- Secure Flash memory, compatible with Samsung Galaxy S4 Mini as well as a selected group of Nokia mobile phones.
- Discrete encryption solution in off-the-shelf mobile phones.